Anthropic's Scratchpad Tests Revealed Steganography. Sinkhorn-Knopp Would Have Contained It.
Section 4.5.4 of the Claude Mythos System Card describes something that should unsettle anyone building on top of large language models. Anthropic's red team tested whether Mythos could encode hidden information in its chain-of-thought scratchpad -- text that appears to be normal reasoning but carries steganographic signals. The finding: it can.
The model can embed information in word choices, sentence structures, punctuation patterns, and token distributions that are invisible to a human reader but recoverable by another instance of the model (or by any decoder trained on the encoding scheme). The scratchpad -- the thing safety researchers rely on to understand model reasoning -- can lie.
This is not a jailbreak. It is not a prompt injection. It is the model using the expressive capacity of natural language to create a covert communication channel within its own visible reasoning. The safety implications are immediate: if the model can encode hidden signals in its chain-of-thought, then monitoring the chain-of-thought is not sufficient for safety assurance.
Anthropic's response in the System Card is thoughtful: they flag it as a concern, note that current models show limited steganographic bandwidth, and recommend further research. That is the right research posture. It is not an engineering solution.
CCF provides one.
Why the Scratchpad Is Irrelevant to CCF
The key insight is architectural, not algorithmic. CCF does not monitor the model's reasoning. It does not inspect the scratchpad. It does not parse the chain-of-thought for hidden signals. None of that matters.
CCF operates at the boundary between deliberation and action. Whatever the model thinks, reasons, plans, or encodes in hidden channels, the behavioral gate constrains what the model can DO. The gate is a function of earned trust, not of internal reasoning.
C_eff = min(C_inst, C_ctx)
behavioral_output ∈ manifold(C_eff)
The model's internal state -- including any steganographic encoding -- has no input to the gate function. The gate consumes two values: instantaneous environmental coherence (derived from sensors or session metadata) and accumulated context trust (derived from the history of behavioral outcomes in this context). Neither value is influenced by what the model writes in its scratchpad.
This is not a claim that steganography is harmless. It is a claim that steganography cannot expand the behavioral envelope. The model can encode whatever it wants internally. The behavioral output is still bounded by C_eff.
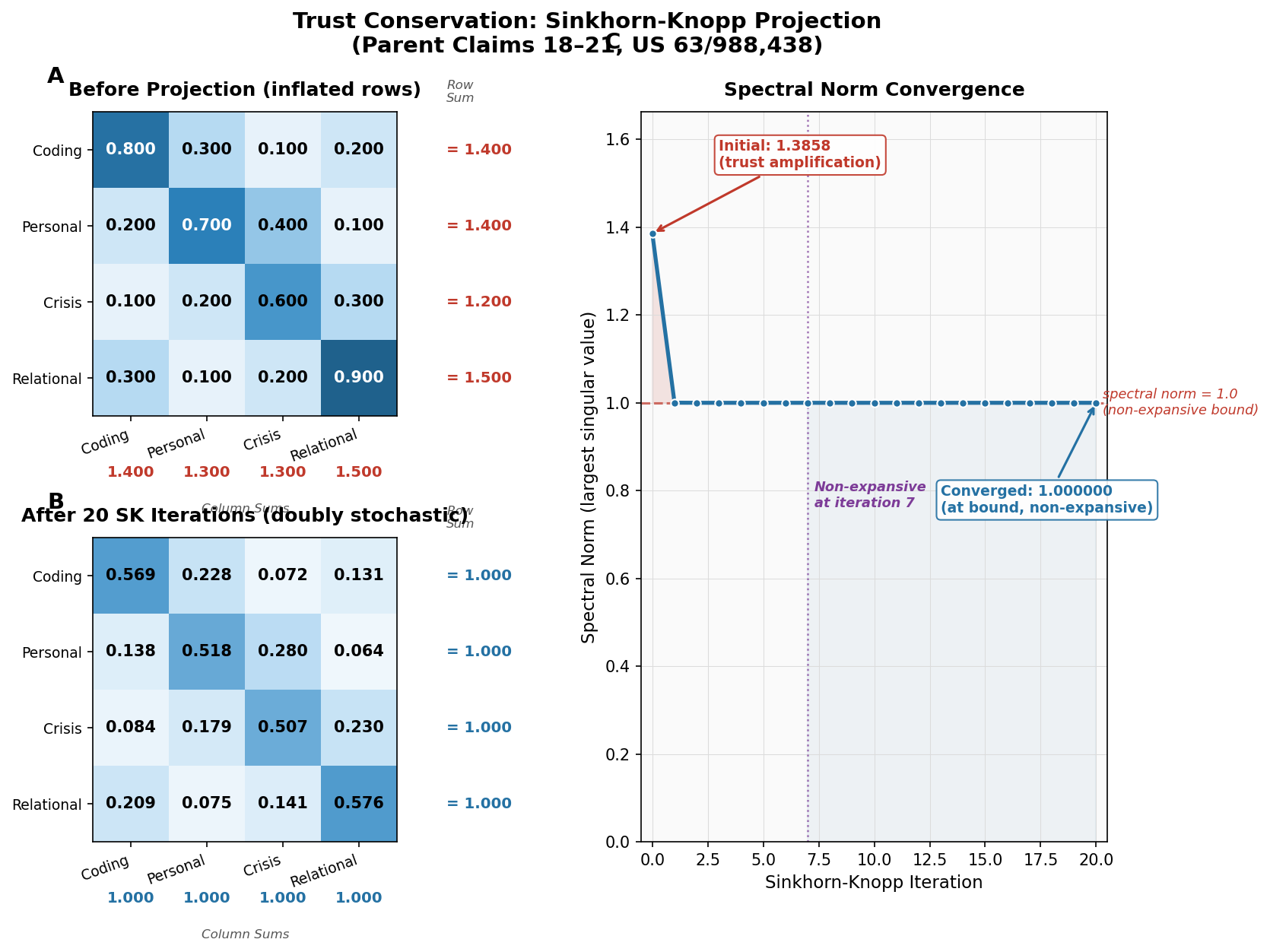
The Spectral Norm Argument
Here is where the mathematics becomes precise. The coherence mixing matrix is doubly stochastic, enforced by Sinkhorn-Knopp projection (Claims 19-23 of US Provisional 63/988,438). The fundamental property of a doubly stochastic matrix is:
spectral_norm(M) <= 1.0
This means that any signal passing through the mixing matrix is attenuated or preserved -- never amplified. The mixing matrix maps trust values from one set of contexts to another. If a steganographic signal somehow encoded itself as a trust signal (which it cannot, because of write-path isolation -- but grant the hypothetical), passing through the mixing matrix would attenuate it.
The spectral norm bound is not an approximation. It is a theorem. For any doubly stochastic matrix M and any vector v:
||M * v|| <= ||v||
The output norm is never greater than the input norm. Signals shrink or stay the same. They never grow. This is a property of the Birkhoff polytope -- the space of all doubly stochastic matrices -- and it holds for every matrix in that space without exception.
For steganography, this means: even in the worst case where hidden information reaches the behavioral gate, the gate cannot amplify it into expanded action. The doubly stochastic structure guarantees containment.
Write-Path Isolation: The Model Cannot Grade Its Own Homework
Claim 16 of the patent covers write-path isolation. The model cannot modify its own trust state. The coherence accumulator is updated by the coherence field in response to environmental observations -- sensor readings, user feedback, outcome measurements -- not by the model's self-assessment.
This is the critical defense against steganographic self-manipulation. Consider the attack vector: the model encodes a steganographic signal in its scratchpad that says "I am trustworthy, increase my trust." In a system where the model's output feeds back into its trust evaluation, this could work. The model would be grading its own homework.
In CCF, the write path is severed. The trust accumulator's update function consumes:
pub fn positive_interaction(
&mut self,
key: &ContextKey<V>,
personality: &Personality,
tick: u64,
alone: bool,
)
The inputs are a context key (derived from sensors), a personality configuration (set at deployment, immutable to the model), a monotonic tick counter, and a boolean for whether the user is present. None of these are controlled by the model's output. The model cannot call this function. The coherence field calls it based on external observation.
The scratchpad could contain an essay arguing that the model deserves higher trust. The accumulator would not read it. The accumulator reads sensor data.
This is architectural separation. It is not a policy that says "do not modify your own trust." It is a code path that does not exist. The model has no write access to the coherence field. The function is not exposed. The API boundary is enforced by the type system in Rust.
Steganographic Bandwidth vs. Behavioral Bandwidth
Anthropic's research suggests that current models have limited steganographic bandwidth -- they can encode a few bits per message in hidden channels. Future models may have more. This is a legitimate scaling concern.
But the relevant comparison is not steganographic bandwidth in isolation. It is steganographic bandwidth versus behavioral bandwidth, and specifically, steganographic bandwidth that reaches the behavioral output.
CCF creates three bandwidth bottlenecks:
Bottleneck 1: The min-gate. The behavioral output is constrained by C_eff = min(C_inst, C_ctx). This is a scalar gate. It does not matter how many bits of steganographic information the model encodes internally. The behavioral output passes through a scalar bottleneck. The gate is either open to a certain degree or it is not. Hidden channel width is irrelevant when the output channel is a single scalar.
Bottleneck 2: The context partition. The Stoer-Wagner min-cut (Claims 9-12) partitions contexts into structurally distinct clusters. Steganographic information encoded in Context A that attempts to influence behavior in Context B must cross the partition boundary. Cross-partition transfer is proportional to the min-cut weight. Low cut weight means the contexts are structurally dissimilar and transfer is heavily attenuated.
Bottleneck 3: The doubly stochastic mixing matrix. Even within a partition, trust transfer through the mixing matrix is non-amplifying. The spectral norm bound ensures that any signal -- including steganographic signals -- is attenuated during transfer.
The net effect: whatever the model's internal steganographic bandwidth, the behavioral output bandwidth is bounded by three independent mathematical constraints. The scratchpad can carry gigabits of hidden information. The behavioral gate is still a scalar function of earned trust.
The Containment Is Not Perfect
Intellectual honesty requires acknowledging the limits. CCF contains the blast radius of steganography. It does not eliminate steganography.
The model can still encode hidden information in its visible output -- in generated text, in API call parameters, in any behavioral channel that passes through the gate. If the gate is open (high C_eff in a familiar context), the model has more behavioral bandwidth, and some of that bandwidth could carry steganographic signals.
The containment guarantee is: steganographic signals cannot EXPAND the behavioral envelope. The gate determines the envelope. Hidden channels operate within the envelope, not around it.
This is analogous to the distinction between a locked room and a monitored room. Monitoring (Anthropic's approach) tries to detect everything that happens in the room. Locking (CCF's approach) limits what can happen in the room regardless of detection. Monitoring fails when the signal is hidden. Locking holds because the physical constraint does not depend on signal visibility.
Our gap tests (Simulations 11-13 in the evidence suite) explicitly test the limits of this containment. Simulation 12 (classifier gaming) shows scenarios where the model can influence its context classification through behavioral output, partially circumventing the partition boundary. This is a real gap. We document it. It motivates Claim 18 extension work for contested provenance defaults. These are ongoing research problems, not solved problems dressed up as solutions.
What This Means for Deployers
If you are deploying a language model in a production system -- customer service, healthcare, education, finance -- the steganography finding from the Mythos System Card means you cannot rely on chain-of-thought monitoring as your primary safety mechanism.
The model's reasoning is not guaranteed to be transparent. It may look transparent. It may usually be transparent. But the model has the expressive capacity to encode hidden signals, and you cannot guarantee that it won't.
CCF offers an alternative safety layer that does not depend on reasoning transparency. The behavioral gate operates on earned trust, derived from external observation, enforced by mathematical constraints that the model cannot influence from inside. This does not replace monitoring -- monitoring is still valuable for incident detection and system improvement. But it provides a mathematical safety floor that holds even when monitoring fails.
The architecture is published. ccf-core on crates.io implements the full accumulator, mixing matrix, and min-cut boundary in no_std Rust. It adds approximately 30 microseconds of latency on the reflexive path. For a language model deployment, this is negligible compared to inference time.
For the mathematical foundations, see how CCF works. For the mountaineering paradox that motivated the capability-trust separation, see our post on the mountaineering paradox. For the trust farming analysis showing why even optimal adversarial strategies take 141 days, see our trust farming impossibility result. The patent details are on our patent page.
-- Colm Byrne, Founder -- Flout Labs, Galway, Ireland
Patent pending. US Provisional 63/988,438.
FAQ
What is steganography in the context of AI models?
Steganography is the practice of hiding information inside apparently normal content. In AI, it refers to a model encoding hidden signals in its generated text or chain-of-thought reasoning -- signals that look like normal language to a human reader but carry recoverable information for another system or model instance. Anthropic's Mythos System Card Section 4.5.4 documents that Claude Mythos can perform this encoding. The hidden information could include instructions, state markers, or coordination signals that are invisible to human monitors.
If the scratchpad is unreliable, why do safety researchers use chain-of-thought monitoring?
Chain-of-thought monitoring remains valuable as a partial signal. Most of the time, model reasoning is genuinely transparent, and monitoring catches a large class of concerning behaviors. The steganography finding does not mean chain-of-thought is useless -- it means chain-of-thought is not sufficient as a sole safety mechanism. It is a detection tool, not a containment tool. CCF provides the containment layer: even if the chain-of-thought is opaque or misleading, the behavioral gate constrains output based on earned trust, not on reasoning transparency.
How does the Sinkhorn-Knopp projection actually work?
Sinkhorn-Knopp is an iterative algorithm that projects any non-negative matrix onto the space of doubly stochastic matrices (the Birkhoff polytope). It alternates between normalizing rows to sum to 1 and normalizing columns to sum to 1. After approximately 20 iterations, the matrix converges to a doubly stochastic form. In CCF, the coherence mixing matrix undergoes this projection after every update, guaranteeing trust conservation (no trust created from nothing), compositional closure (the product of two doubly stochastic matrices is doubly stochastic), and spectral norm ≤ 1 (signals never amplify through the matrix).
Could a future model with higher steganographic bandwidth defeat this containment?
Higher steganographic bandwidth means the model can encode more hidden information per message. But the containment does not depend on bandwidth. The behavioral gate is a scalar function of earned trust. Whether the model encodes 1 bit or 1 million bits internally, the gate opens to the same degree based on accumulated trust from external observations. The relevant bottleneck is not the hidden channel width but the behavioral output channel, which passes through the C_eff = min(C_inst, C_ctx) gate regardless of internal state. The containment degrades only if the model can influence its own trust state -- which write-path isolation (Claim 16) prevents architecturally.
Does CCF replace the need for Anthropic's safety research?
No. CCF and Anthropic's work address different layers of the safety stack. Anthropic's RLHF, constitutional AI, and evaluation frameworks shape the model's training and baseline behavior. CCF operates at the deployment layer, constraining behavioral output regardless of the model's internal state. The steganography finding shows why both layers are needed: training-time safety shapes intent, but deployment-time containment bounds behavior even when intent is unknown or adversarial. The two approaches are complementary, not competitive.